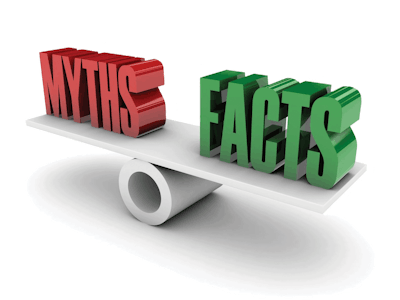
A recent article from FierceHealthcare referenced a speech from Seth Carmody, senior program manager for medical device cybersecurity at the FDA, in which he addressed common misconceptions regarding medical device security. Here’s a summary:
Myth: The FDA is solely responsible for medical device cybersecurity.
Truth: Several agencies are responsible including the Department of Homeland Security and the Department of Health and Human Services.
Myth: Medical device manufacturers can’t issue updates or cybersecurity fixes without FDA approval.
Truth: Manufacturers can apply routine cybersecurity updates at any time for any reason without FDA approval. But, according to the FDA’s premarket guidance, security updates that could cause adverse health consequences are not considered “routine”.
Myth: The FDA tests medical devices for cybersecurity vulnerabilities.
Truth: The FDA doesn’t test devices at all. FDA’s guidance states, “postmarket cybersecurity information may originate from an array of sources including independent security researchers, in-house testing, suppliers of software or hardware technology, health care facilities, and information sharing and analysis organizations.”
Myth: Healthcare organizations can’t patch or update a device for cybersecurity reasons.
Truth: The FDA prefers a collaborative approach to device updates, but organizations can issue patches or updates on their own if they assume responsibility and understand the risks.